A Note to our Customers and Partners in the Middle East
More InformationCVE-2023-31190
DroneScout ds230 Remote ID receiver from BlueMark Innovations is affected by an Improper Authentication vulnerability during the firmware update procedure.
The firmware update procedure ignores and does not check the validity of the TLS certificate of the HTTPS endpoint from which the firmware update package (.tar.bz2 file) is downloaded. An attacker with the ability to put himself in a Man-in-the-Middle situation can trick the DroneScout ds230 to install a crafted malicious firmware update.
July 10, 2023
The vulnerability affects: DroneScout ds230 from firmware version 20211210-1627 to firmware version 20230329-1042
CVE-2023-31190
CVSS:3.1/AV:N/AC:H/PR:N/UI:N/S:U/C:H/I:H/A:H
8.1
Update to firmware version newer than 20230329-1042
Nicolò Facchi of Nozomi Networks
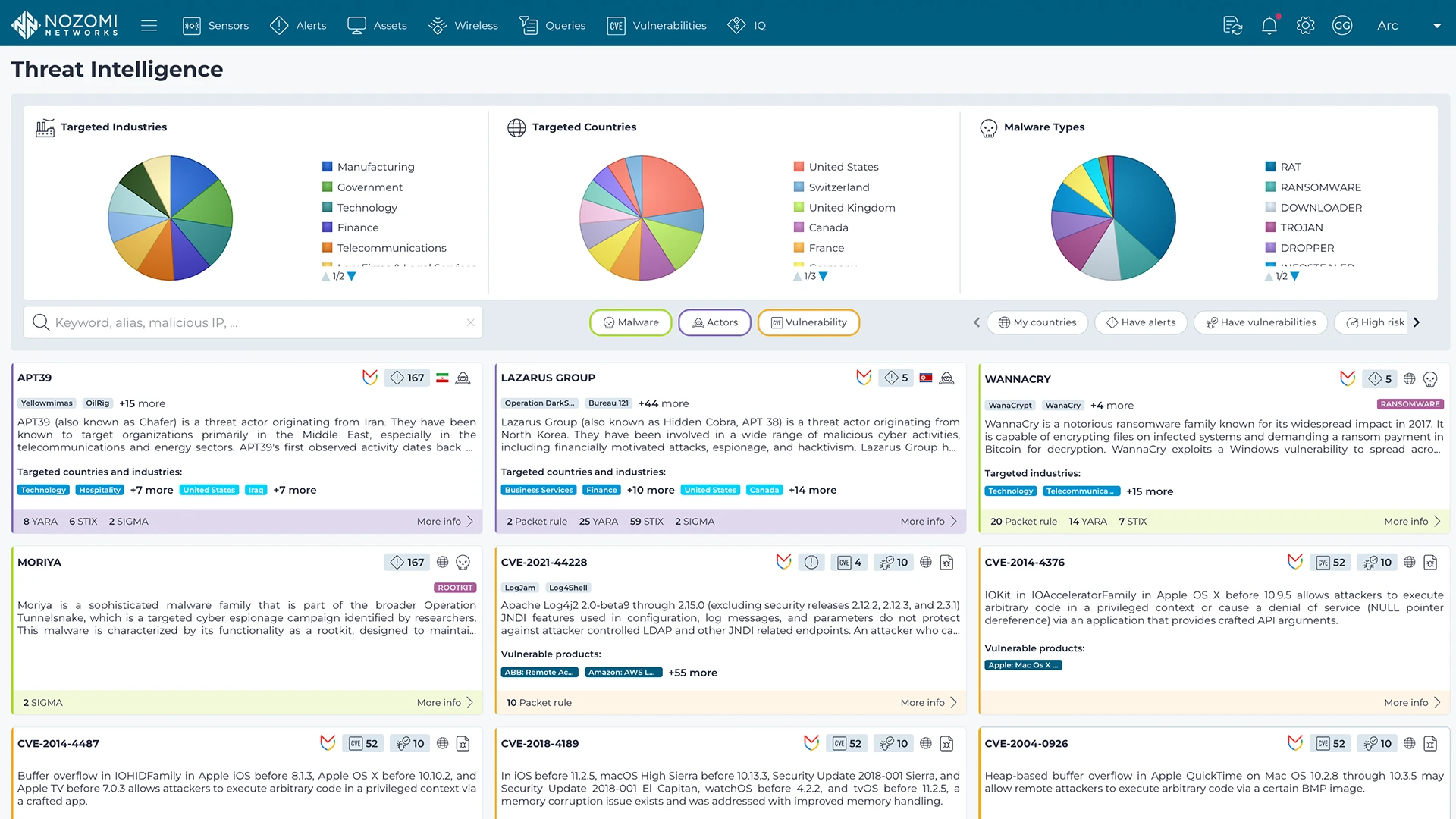
Nozomi Networks Labs curates threat and vulnerability insights that are continuously fed into the Nozomi Networks platform to ensure our sensors can detect existing and emerging threats and vulnerabilities that threaten customers environments.
Learn more