A Note to our Customers and Partners in the Middle East
More InformationCVE-2023-51456
A Improper Input Validation issue affecting the v2_sdk_service running on a set of DJI drone devices on the port 10000 could allow an attacker to trigger an out-of-bound read/write into the process memory through a crafted payload due to a missing input sanity check in the v2_pack_array_to_msg function implemented in the libv2_sdk.so library imported by the v2_sdk_service binary implementing the service, potentially leading to a memory information leak or an arbitrary code execution.
An adjacent attacker may reach arbitrary code execution on the v2_sdk_service running on the drone.
March 29, 2024
This issue affects: Mavic 3 Pro below version 01.01.0300, Mavic 3 below version 01.00.1200, Mavic 3 Classic below version 01.00.0500, Mavic 3 Enterprise below version 7.01.10.03, Matrice 300 below version 57.00.01.00, Matrice M30 below version 07.01.0022, Mini 3 Pro below version 01.00.0620
CVE-2023-51456
CVSS:3.1/AV:A/AC:H/PR:L/UI:R/S:U/C:H/I:H/A:H
6.8
Upgrade the firmware of impacted models to the latest available version
Diego Giubertoni of Nozomi Networks
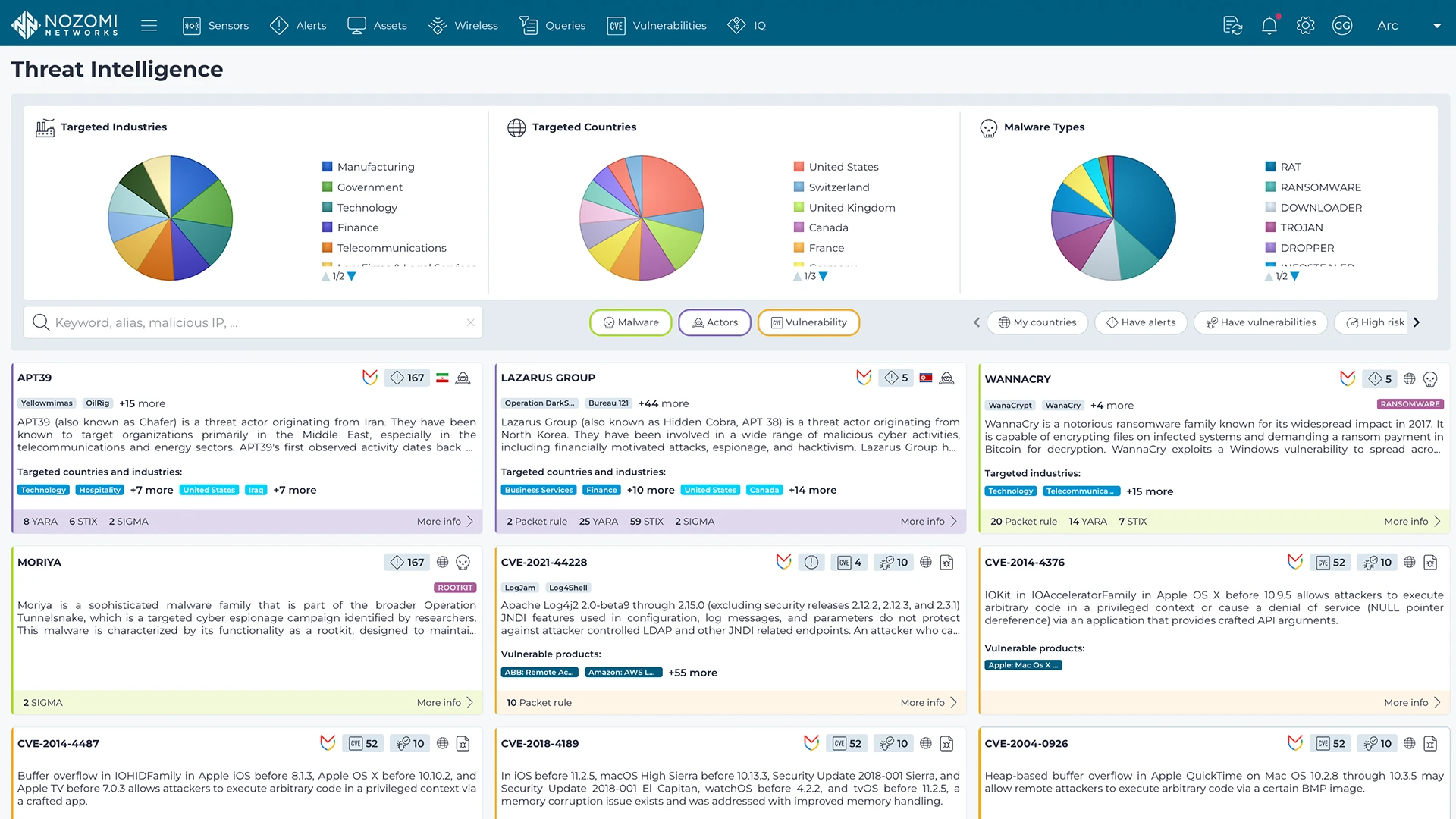
Nozomi Networks Labs curates threat and vulnerability insights that are continuously fed into the Nozomi Networks platform to ensure our sensors can detect existing and emerging threats and vulnerabilities that threaten customers environments.
Learn more