A Note to our Customers and Partners in the Middle East
More InformationCVE-2024-12011
A CWE-126 “Buffer Over-read” was discovered affecting the 130.8005 TCP/IP Gateway running firmware version 12h. The information disclosure can be triggered by leveraging a memory leak affecting the web server.
A remote unauthenticated attacker can exploit this vulnerability in order to leak valid authentication tokens from the process memory associated to users currently logged to the system and bypass the authentication mechanism.
February 17, 2025
This issue affects: Zettler 130.8005 version 12h.
CVE-2024-12011
CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:L/A:L
7.6
It is recommended to segregate the host to a management VLAN where only authorized clients have the ability to interact with it.
Diego Zaffaroni of Nozomi Networks
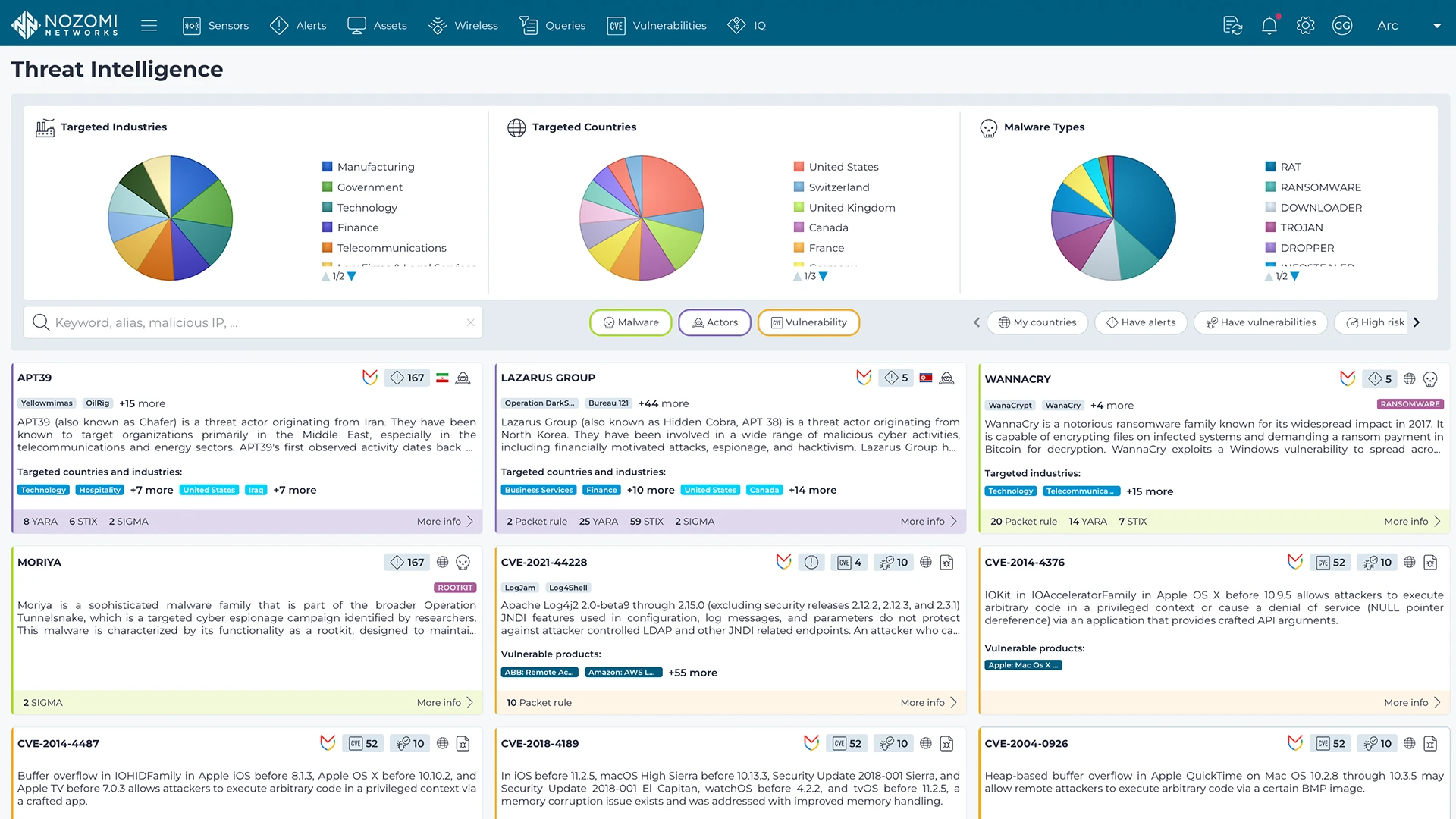
Nozomi Networks Labs curates threat and vulnerability insights that are continuously fed into the Nozomi Networks platform to ensure our sensors can detect existing and emerging threats and vulnerabilities that threaten customers environments.
Learn more