A Note to our Customers and Partners in the Middle East
More InformationCVE-2024-31199
A “CWE-79: Improper Neutralization of Input During Web Page Generation ('Cross-site Scripting')” allows malicious users to permanently inject arbitrary Javascript code.
Arbitrary Javascript code can be executed in the context of the victim browser, therefore allowing the execution of any operation on behalf of the victim user.
July 7, 2023
Sensor Net Connect V2 (FW version 2.24)
CVE-2024-31199
CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H
8.8
No official patch available from vendor. Implement strict access controls for the temperature monitoring infrastructure. This includes preventing regular clients from accessing the web configuration interface, thereby limiting potential points of exploitation. Conduct regular and thorough reviews of logs and user accounts on systems running the Thermoscan IP software. This will help identify and address any suspicious activities early, ensuring that any potential security breaches are caught and remediated swiftly.
Diego Zaffaroni of Nozomi Networks
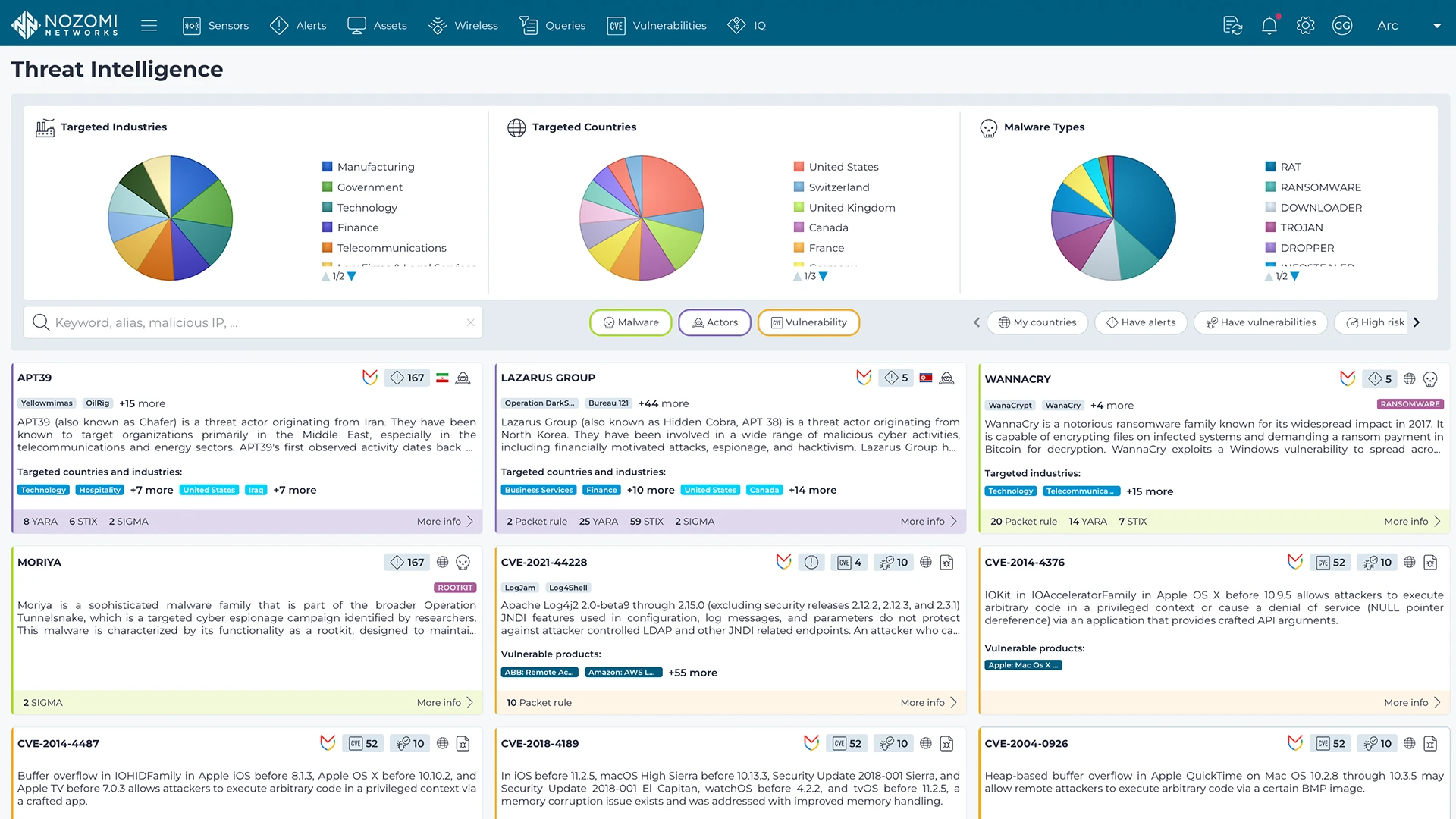
Nozomi Networks Labs curates threat and vulnerability insights that are continuously fed into the Nozomi Networks platform to ensure our sensors can detect existing and emerging threats and vulnerabilities that threaten customers environments.
Learn more