A Note to our Customers and Partners in the Middle East
More InformationCVE-2025-26370
A CWE-862 "Missing Authorization" in maxprofile/user-groups/routes.lua in Q-Free MaxTime less than or equal to version 2.11.0 allows an authenticated (low-privileged) attacker to remove privileges from user groups via crafted HTTP requests.
An authenticated low-privileged remote attacker may remove privileges from user groups, potentially impeding access to important resources.
February 11, 2025
This issue affects: Q-Free MaxTime less than or equal to version 2.11.0.
CVE-2025-26370
CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:H/A:L
7.1
An official solution has not been communicated by the vendor. The vulnerability can be exploited by authenticated remote attackers. As a temporary solution, until a patch is released, it is highly recommended to: 1) periodically review the configuration of users and groups on the management web application exposed by devices running Q-Free MaxTime less than or equal to version 2.11.0 and confirm that all settings are as expected; 2) review all accounts on the same management web application and delete unnecessary ones.
Diego Giubertoni of Nozomi Networks
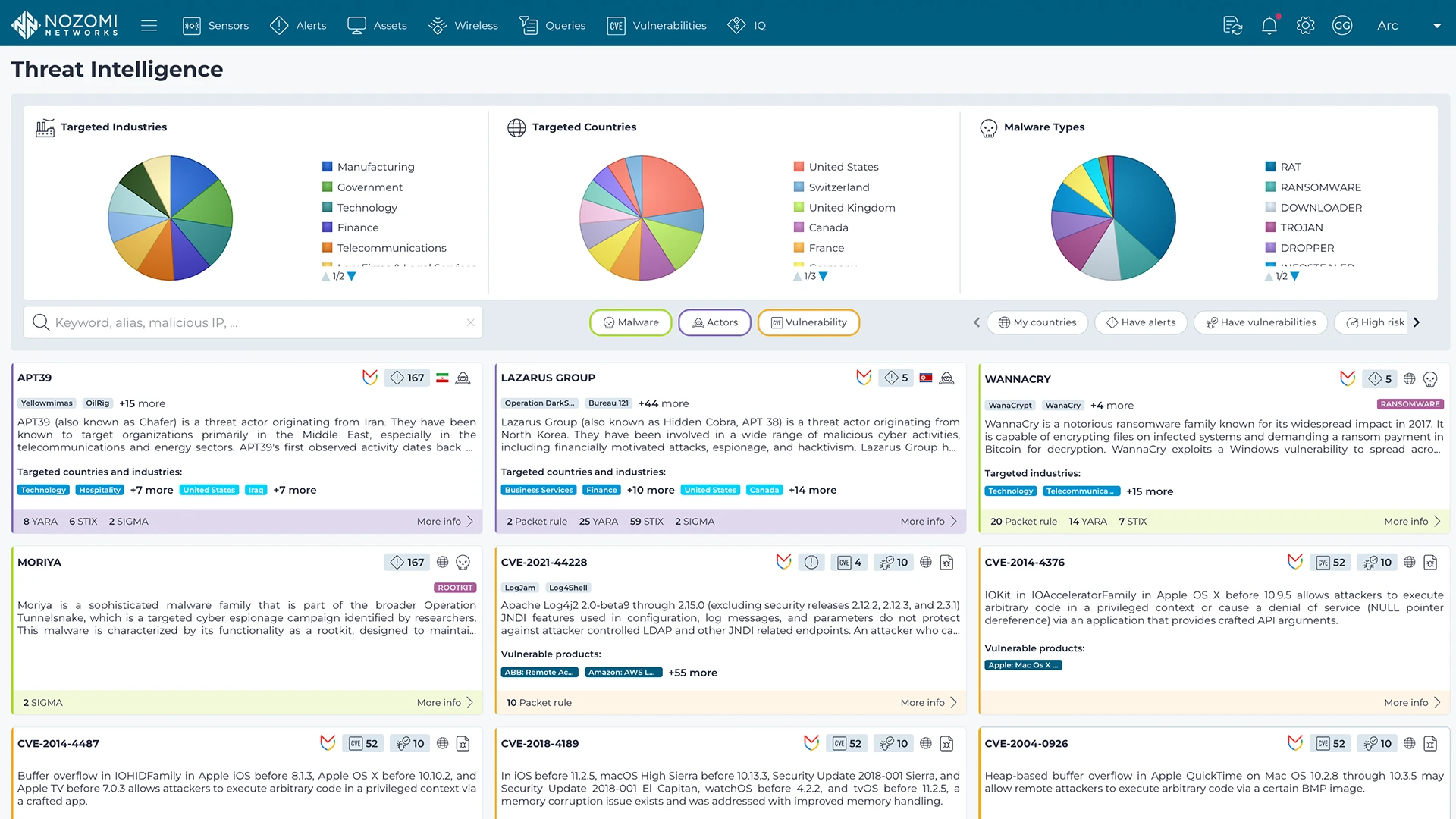
Nozomi Networks Labs curates threat and vulnerability insights that are continuously fed into the Nozomi Networks platform to ensure our sensors can detect existing and emerging threats and vulnerabilities that threaten customers environments.
Learn more